In today’s dynamic business landscape, virtualization has emerged as a powerful technology that enables organizations to optimize resource utilization, enhance scalability, and streamline IT operations. However, implementing virtualization requires careful planning, strategic execution, and adherence to best practices to maximize its benefits. In this blog post, we’ll explore the key best practices for successfully implementing Virtualization Best Practices for Your Organization.
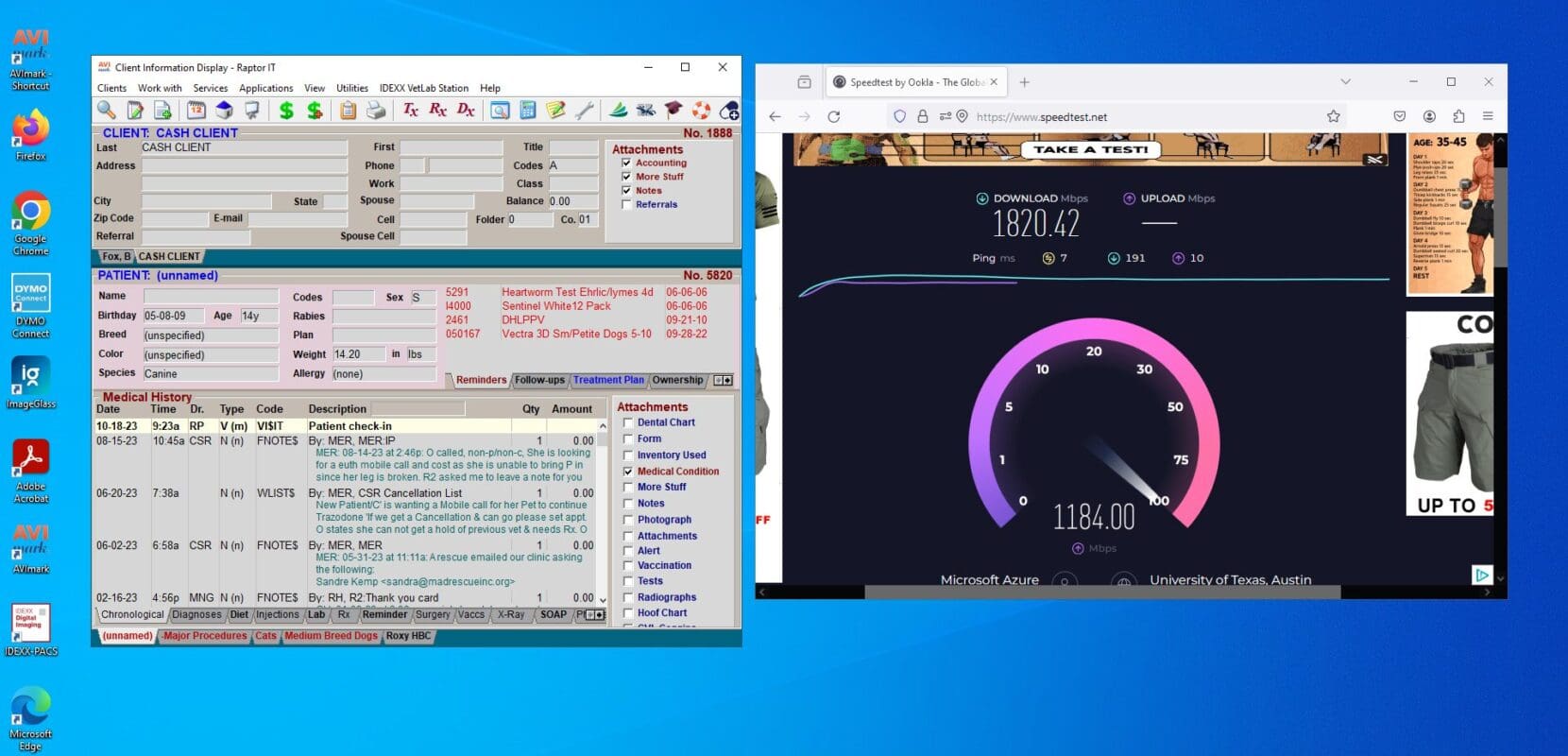
- Assess Your Infrastructure: Before embarking on a virtualization project, conduct a comprehensive assessment of your existing IT infrastructure. Evaluate factors such as hardware compatibility, network bandwidth, storage capacity, and application dependencies to determine the feasibility and scope of virtualization.
- Define Clear Objectives: Clearly define your organization’s goals and objectives for implementing virtualization. Whether it’s reducing hardware costs, improving disaster recovery capabilities, or enhancing scalability, having a clear understanding of your objectives will guide the virtualization strategy and implementation process.
- Choose the Right Hypervisor: Selecting the appropriate hypervisor is crucial for the success of your virtualization initiative. Evaluate different hypervisor options based on factors such as performance, scalability, management capabilities, and compatibility with your existing infrastructure.
- Plan for Capacity and Performance: Proper capacity planning is essential to ensure that your virtualized environment can meet the demands of your organization. Consider factors such as workload requirements, resource allocation, and growth projections when planning capacity and performance for your virtualized infrastructure.
- Implement Robust Security Measures: Security should be a top priority when implementing virtualization. Implement robust security measures such as network segmentation, access controls, encryption, and regular security updates to protect your virtualized environment from cyber threats and unauthorized access.
- Optimize Resource Allocation: Efficient resource allocation is critical for maximizing the performance and cost-effectiveness of your virtualized environment. Utilize tools and technologies for dynamic resource allocation, workload balancing, and performance monitoring to optimize resource utilization and minimize wastage.
- Establish Backup and Disaster Recovery Plans: Implement comprehensive backup and disaster recovery plans to safeguard your virtualized environment against data loss, system failures, and other disasters. Utilize backup solutions, replication technologies, and offsite storage to ensure data availability and business continuity.
- Train Your IT Staff: Provide adequate training and resources to your IT staff to ensure they have the knowledge and skills required to manage and maintain the virtualized environment effectively. Invest in training programs, certifications, and ongoing education to keep your IT team abreast of the latest virtualization technologies and best practices.
- Monitor and Maintain Your Environment: Regular monitoring and maintenance are essential for ensuring the health, performance, and security of your virtualized environment. Implement monitoring tools and processes to proactively identify and address issues, perform regular maintenance tasks, and keep your virtualized infrastructure running smoothly.
- Continuously Evaluate and Improve: Virtualization is an evolving technology, and it’s important to continuously evaluate and improve your virtualized environment to adapt to changing business needs and technological advancements. Regularly review your virtualization strategy, performance metrics, and security posture to identify areas for optimization and enhancement.
By following these best practices, your organization can successfully implement virtualization and reap the benefits of improved efficiency, scalability, and flexibility in your IT infrastructure. With careful planning, strategic execution, and a focus on best practices, virtualization can become a cornerstone of your organization’s IT strategy. Master Virtualization Best Practices for Your Organization with Raptor IT Solutions.