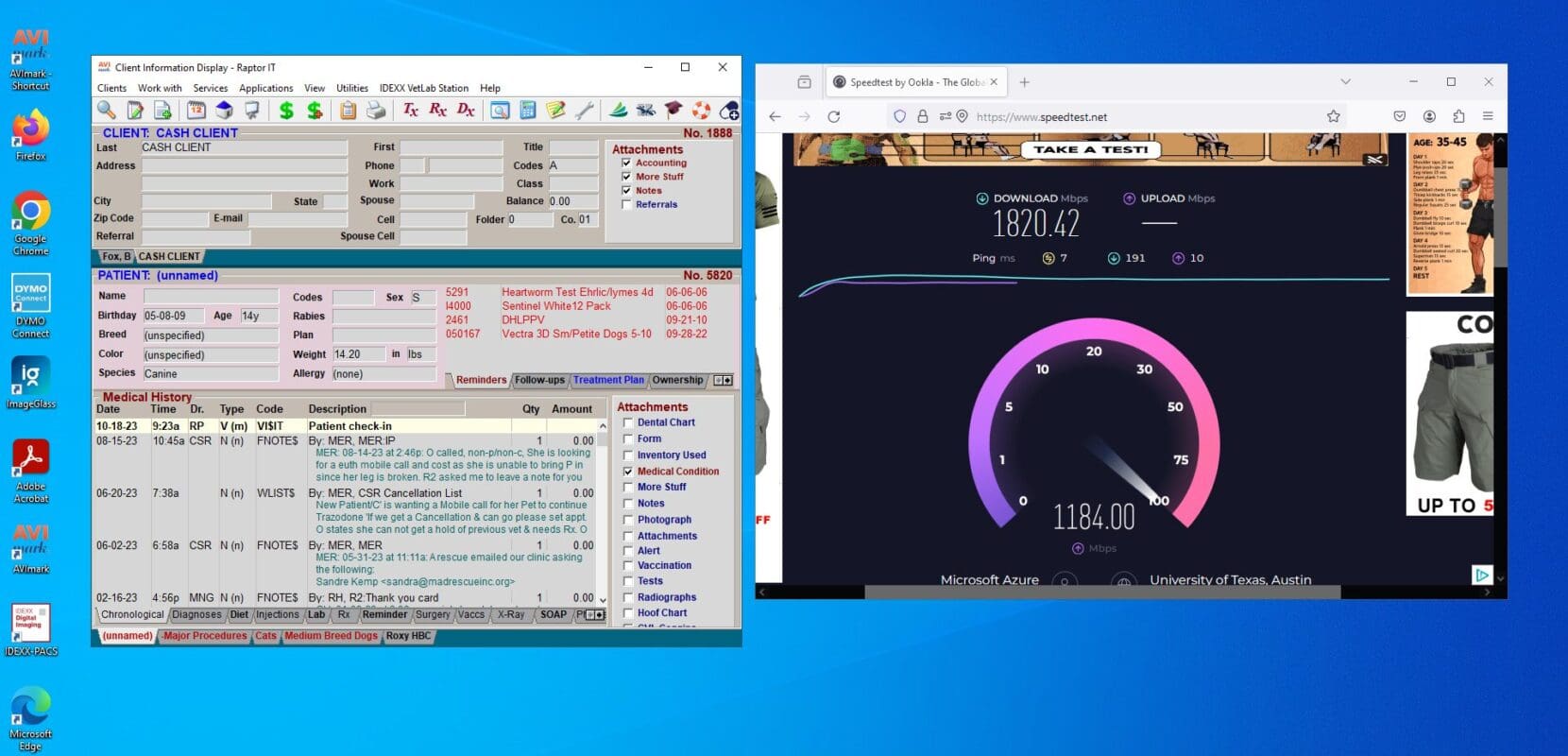
In the ever-evolving landscape of veterinary practice management, transitioning Avimark to the cloud emerges is a game-changer. Can it be done? Raptor IT Solutions has achieved it! This blog explores the benefits, challenges, and transformative impact of migrating Avimark to the cloud for enhanced efficiency and seamless veterinary operations.
Introduction: Navigating the Shift to Cloud-Based Veterinary Management
Embark on a journey to explore the profound impact of transitioning Avimark, a leading veterinary software, to the cloud. This blog sheds light on the motivations behind this shift, promising a paradigm shift in how veterinary practices manage their operations.
1. Enhanced Accessibility and Flexibility
Dive into the advantages of cloud-based Avimark, offering practitioners the freedom to access vital data and manage operations from any location. Discover how this enhanced accessibility fosters flexibility, making veterinary management more dynamic and responsive.
2. Improved Collaboration and Communication
Explore the collaborative potential of a cloud-based system, revolutionizing communication within veterinary teams. Uncover how cloud solutions facilitate real-time collaboration, enabling seamless communication between staff members and enhancing overall practice efficiency.
3. Secure Data Management and Compliance
Delve into the robust security measures inherent in cloud-based systems, ensuring the confidentiality and integrity of sensitive veterinary data. Learn how cloud solutions align with industry compliance standards, providing peace of mind for practitioners and safeguarding patient information.
4. Scalability for Growing Practices
Navigate the scalability of cloud-based, tailored to accommodate the evolving needs of growing veterinary practices. Understand how cloud solutions adapt effortlessly to an expanding clientele, supporting practices in their journey towards greater success.
5. Cost-Efficiency and Resource Optimization
Explore the cost-effectiveness of migrating, eliminating the need for extensive on-premise infrastructure. Uncover how cloud solutions optimize resources, offering veterinary practices a streamlined and economical approach to data management.
6. Seamless Integration with Third-Party Applications
Understand the ease with which cloud-based Avimark integrates with third-party applications, enhancing the overall functionality of veterinary practices. Discover the potential for a comprehensive ecosystem that complements Avimark, providing practitioners with a holistic solution.
7. Robust Backup Solutions and Minimal Maintenance
Examine the crucial role of backups in a cloud-based Avimark system, ensuring the safety and recoverability of essential data. Learn how streamlined maintenance in the cloud reduces the burden on veterinary staff, allowing them to focus on patient care rather than intricate IT tasks.
Conclusion: Transforming Veterinary Management with Cloud-Based Avimark
As the journey through the advantages of cloud-based Avimark concludes, grasp the transformative potential that awaits veterinary practices. From enhanced accessibility to fortified security measures, the cloud redefines veterinary management, ensuring practices stay ahead in the digital age.
Ready to elevate your veterinary practice with cloud-based Avimark? Explore seamless integration and enhanced efficiency with Raptor IT Solutions. Contact us today at 469-589-4008 to embark on a transformative journey in veterinary management.